Whitelisting
How to Whitelist a User/Device in ThreatLens
Whitelisting allows trusted users or devices to continue accessing the application, even if they are flagged with certain threat indicators.
Step-by-Step Process
- Navigate to ThreatLens
Open the ThreatLens module from your dashboard. - Access Latest Threat Activity
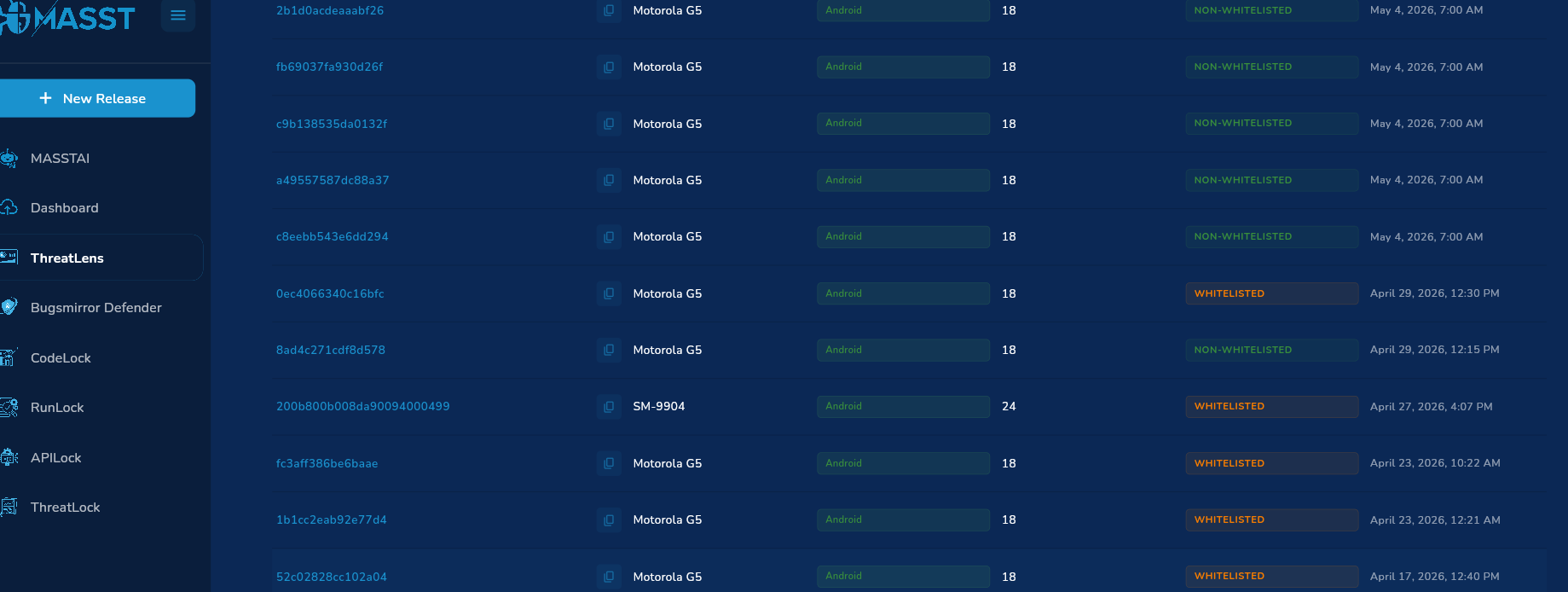
Go to the Latest Threat Activity section to view all detected threats. - Identify the Target Device
- Review the list of devices flagged with at least one threat or malicious indicator.
- Use the search bar to quickly find a specific device by name or device ID.
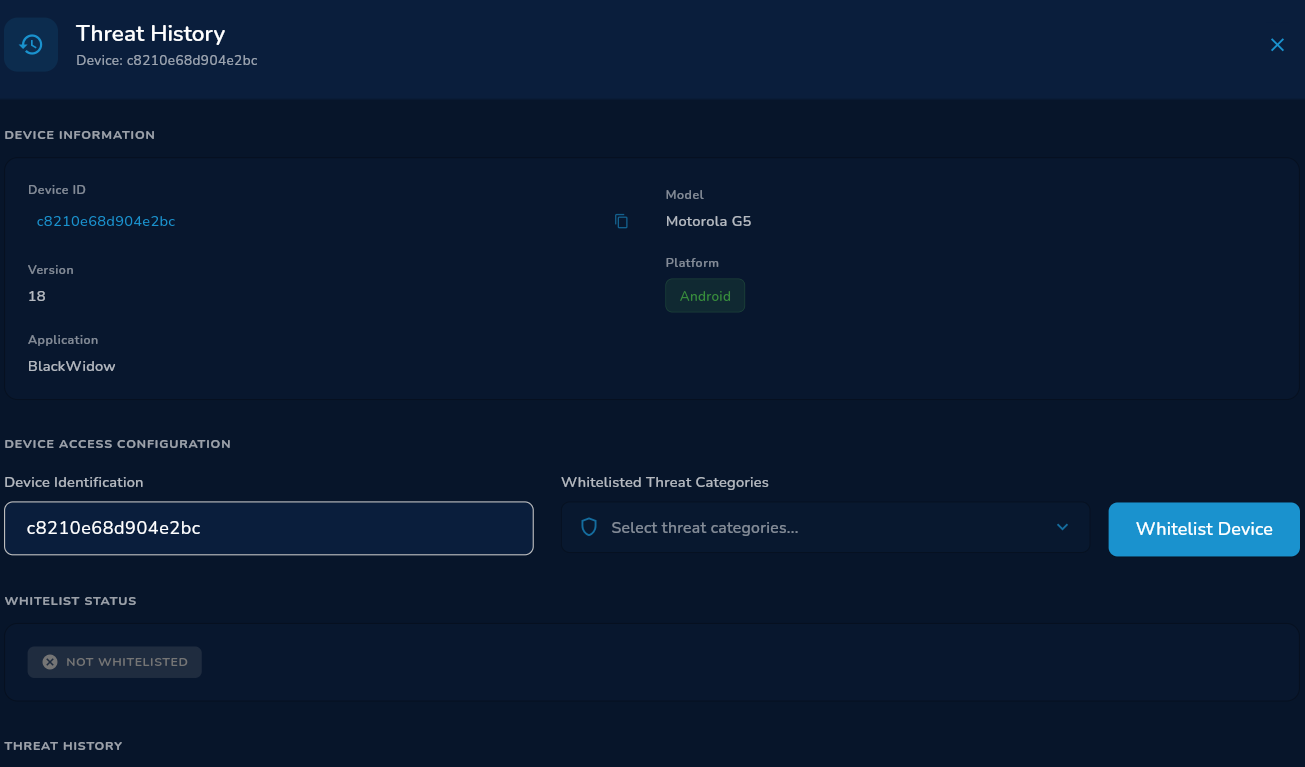
- Select the Device
Click on the device you want to whitelist. - Review Threat Details
Analyze the device information, including:- Threat ID.
- Threat Group.
- Timespan of detected activity.
- Initiate Whitelisting
Click on the “Whitelist Device” button. - Confirm Action
The system will process the request and display a “Device Whitelisted Successfully” notification. - Verification
- The selected device is now whitelisted.
- Updated status is reflected in the Latest Threat Activity dashboard.
- You can also track the count of whitelisted vs non-whitelisted devices.
Technical Note
Whitelisting overrides automated threat enforcement for specific devices, so it should only be applied to verified and trusted users after proper validation.